|
Web
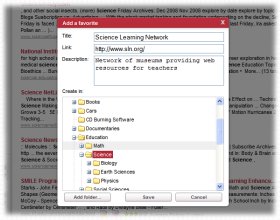
Education
Journal of mobile, embedded and distributed systems ...
Get this from a library! Journal of mobile, embedded and distributed systems.. [Academia de Studii Economice (Romania),;]
Journal of Mobile, Embedded and Distributed Systems ...
COVID-19 Resources. Reliable information about the coronavirus (COVID-19) is available from the World Health Organization (current situation, international travel).Numerous and frequently-updated resource results are available from this WorldCat.org search.OCLC’s WebJunction has pulled together information and resources to assist library staff as they consider how to handle coronavirus ...
Journal of Mobile, Embedded and Distributed Systems - JMEDS
Refbacks. There are currently no refbacks. Journal of Mobile, Embedded and Distributed Systems (JMEDS) ISSN: 2067 – 4074 (online)
Journal of Mobile, Embedded and Distributed Systems - JMEDS
Rootkits are considered by many to be one of the most stealthy computer malware (malicious software) and pose significant threats. Hiding their presence and activities impose hijacking the control flow by altering data structures, or by using hooks in the kernel.
Approaches on Internet of Things Solutions - Wikisource ...
Figure 1. Internet of Things components. A Smart Object contains IoT data and information, also metadata and software agent code resources, such as application software event handler. Samples of Smart Objects are embedded devices such as Rasberry Pi, Arduino, BeagleBone/Ninja Blocks. The data model for broad interoperability is represented by the Smart Object API.
(PDF) Project Management with IT Security Focus
Project Management with IT Security Focus. Article (PDF Available) · December 2011 ... Journal of Mobile, Embedded and Distributed Systems, vol. III, no. 4, 2011. ISSN 2067 ...
Journal of Mobile, Embedded and Distributed Systems, vol. I, no. 1, 2009 ISSN 2067 – 4074 Key Page 7 If the device sends a encrypted packet over WiFi using WEP in IEEE 802.11 secure architecture then the user insert a symmetric encryption key (the same as the one from
(PDF) Binary Code Disassembly for Reverse Engineering
The disassembly of binary file is used to restore the software application code in a readable and understandable format for humans. Further, the assembly code file can be used in reverse ...
This file is licensed under the Creative Commons Attribution 3.0 Unported license.: You are free: to share – to copy, distribute and transmit the work; to remix – to adapt the work; Under the following conditions: attribution – You must give appropriate credit, provide a link to the license, and indicate if changes were made. You may do so in any reasonable manner, but not in any way ...
Page:Approaches on Internet of Things Solutions.pdf/1 ...
Journal of Mobile, Embedded and Distributed Systems, vol. V, no. 3, 2013 ISSN 2067 – 4074 www.jmeds.eu Approaches on Internet of Things Solutions Cristian TOMA, Cristian CIUREA, Ion IVAN
|